Welcome to
Sensitive Network ™
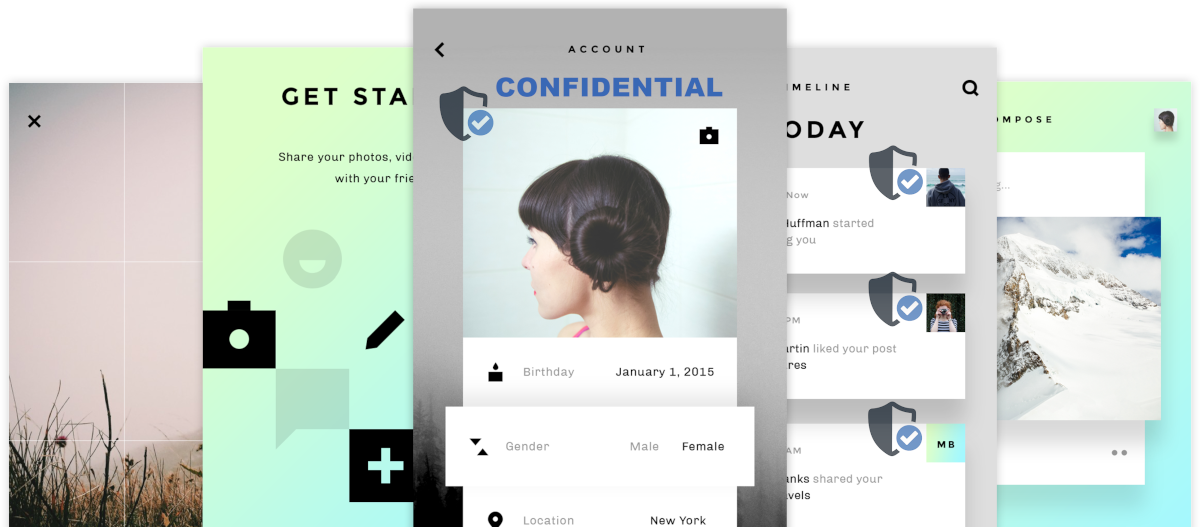
+ Classified Data
+ Confidential Comms
+ Privacy Analytics
+ Zero Trust Security
= You in Control